Contents
- How to change your IP address
- What if I have a static IP address?
- Security Tips
- Links and Further Reading
How to change your IP address
There are times when you need to change your IP address, for instance: after detecting a virus (trojan) or other threat on your computer, being targeted by a hacker, or as a general security measure. It’s good practice to renew your IP address weekly at the very least. Most ISP’s set up their networks and user modems to automatically renew after 7 days (user connections are typically DHCP) however, if you are more technically minded, you can easily change the lease time by logging into your modem and altering the value to a lower number. The value will likely be in seconds or minutes, example: 604800 seconds = 10080 minutes = 7 days.
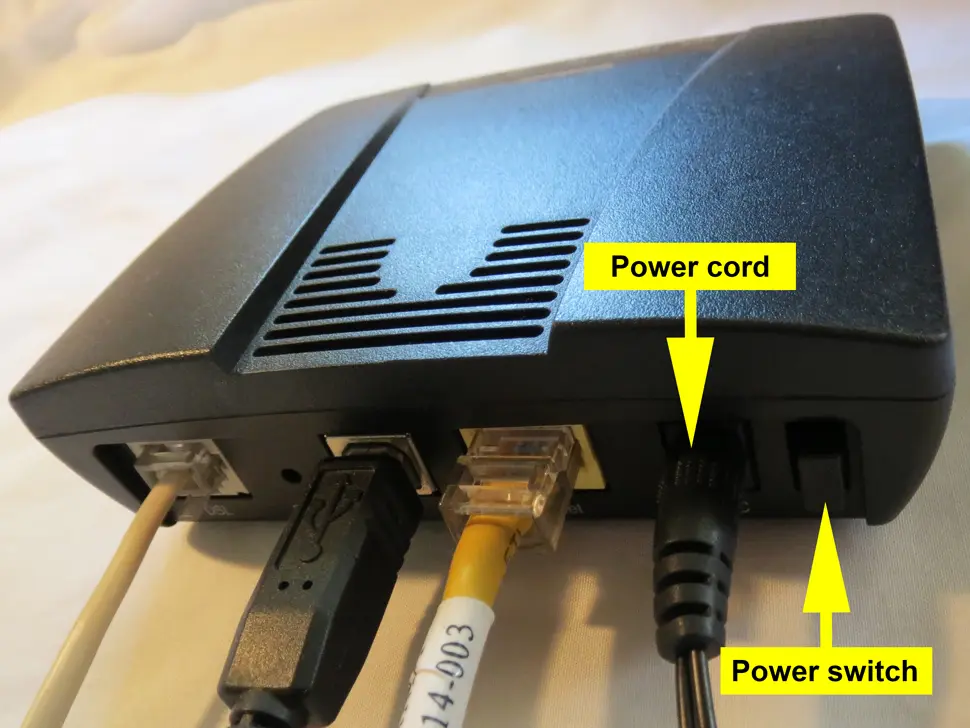
If you need a less complex option, simply power cycling your modem will renew your IP address quickly and easily 99% of the time (assuming DHCP connection). What does power cycling your modem mean? Well, it’s as simple as switching off your modem (or unplugging the power cord), for 60 seconds and then switching it back on again (see example 1.a below). This closes the connection to your ISP, and forces a new IP address negotiation when you switch it back on. You may have to wait up to 5 minutes after power cycling to successfully re-connect to your ISP.
What if I have a static IP address?
If your ISP has assigned you a static IP address, the only way to change it is to call your ISP’s tech support line and ask it be changed. But remember, for whatever reason you had the static IP address assigned initially (such as: running web servers or certain games), you will likely have to change IP settings in those items as well, otherwise data is sent to the wrong IP address.
Can I hide my IP address?
The short answer is yes. There are a number of methods to hide your IP address, and we will look at some below in more detail. For the long answer, continue reading after these examples.
- VPN (Virtual Private Network) – This is the most popular way to hide your IP address and even the country you’re living in. Similar to a Proxy Server, a VPN is an encrypted tunnel between your computer, and a VPN server that could be located in any country. Popular VPN services are IPVanish VPN, ExpressVPN, or NordVPN.
- Proxy Servers – This is probably the most popular method of hiding your IP address. A proxy server is another computer situated between your machine and the internet that simply “passes” all your requests through itself, and sends its own identity (IP address) to the website server, thereby obscuring your information (think Escrow). There are also web-based proxy servers that you simply visit with your web browser and type in the web address.
- Anonymity Networks – Another popular method requiring software installation are anonymity networks. These networks are setup all over the world and any http request can be routed to any number of servers, at any given time. This is known as onion routing. The most popular of this type is Tor.
There are some exceptions and advisories to the above examples…
- Servers (including proxy servers) generally log the real IP address of its users and therefore create a record of your activity. Records can be handed over to authorities if requested by a court of law. There are some proxy servers that specify that they don’t keep any logs, but there is never a 100% guarantee.
- Anonymous proxy servers, renowned as dangerous and not so anonymous. If you have to use a proxy server make sure it is a reputable one (tips: searching forums can show a much information, paid services are sometimes the best).
- Even when you setup and pay for a proxy server or anonymity network service, if your PC or local LAN network is compromised, it’s all for nothing I’m afraid. The NSA/CIA have the most high-tech gadgets at their disposal and can penetrate almost any network they want, so if you wish to stay truly anonymous online, make sure your entire data-flow is secured, from your keyboard, PC, LAN, firewall, modem and all the way to your desired network destination and back again.
Security Tips
Of course, if you are wanting to secure your home or business network to guard against criminals, you have a better chance at achieving this by optimizing a few important aspects of your network like:
- Do not use a static IP address from your ISP unless absolutely necessary
- Have a short DHCP lease time (24 hours) for dynamically assigned IP addresses
- Make sure all PC’s on your network have good antivirus protection that is up-to-date and scanned regularly (between 3 and 7 days between full system scans)
- Make sure you password-protect WiFi/wireless networks
- Enable the guest WiFi network instead of giving out your SSID WiFi password to visitors, most new modems will have the guest network feature
- Always let your antivirus scan USB/SD type cards when inserted into a PC on your network, especially from visitors or unknown sources
- For business networks, setup a dedicated firewall from a reputable company, or have your IT guy setup Smoothwall or IPFire open source firewall solutions to save money
- Use a good Password Manager (Google Chrome and Firefox have built-in password managers which are very secure)
- Never use the same password for different websites. I know it’s difficult, but if your whole life is protected by one password, a criminal will have your bank accounts drained within hours (not to mention what they would do with Facebook, Twitter sites)
- For business networks: get your IT guy to enforce a minimum password length, complexity, and time limit for all your employees
- Lastly, never let your email program automatically download images by default. An image in an email can give a hacker your external and internal IP address and other info, basically a target right into your network and your PC
Although no guarantee, following these basic rules will make it harder for criminals to compromise your network or PC’s.
Comments
There are currently no comments on this article.
Comment